Network access control (NAC) prevents unwanted users and devices from getting access to a corporate or private network.
What is network access control?
The practice of restricting unwanted users and PCs from getting access to a corporate or private network is known as network access control (NAC). NAC ensures that only authenticated users and devices that are authorized and in compliance with security policies can access the network.
The automated elements of a NAC solution are a significant benefit, as they save the time and expenses associated with authenticating and authorizing users and ensuring that their devices are compatible.
Furthermore, cybercriminals are well aware of the rise in endpoint usage and are continuing to build and deploy sophisticated data breach campaigns that attack any weaknesses in corporate networks. With additional endpoints, the attack surface expands, giving fraudsters more opportunity to acquire access.
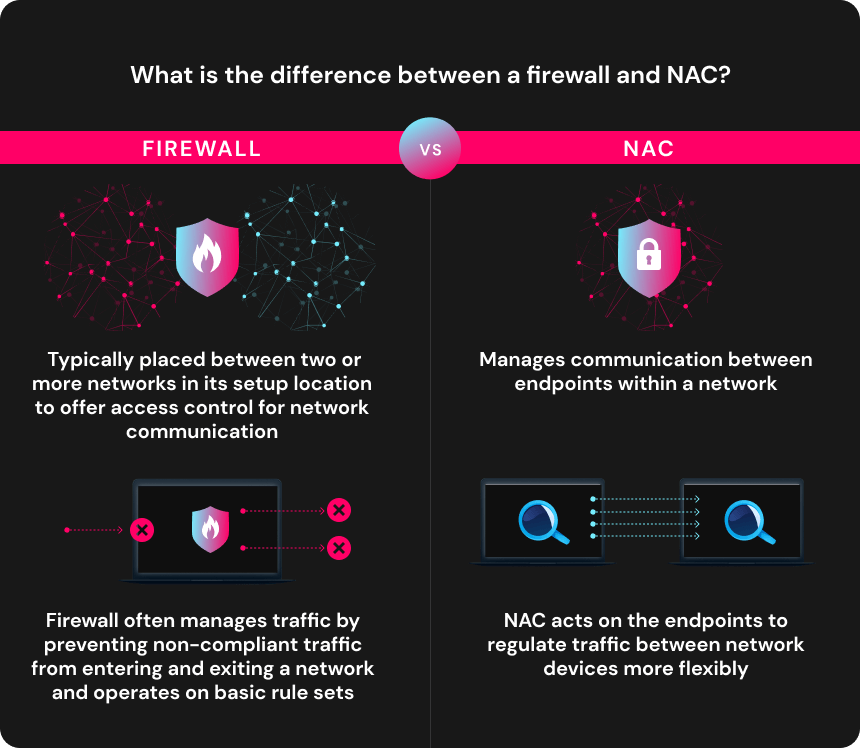
What is the difference between a firewall and NAC?
A firewall is typically placed between two or more networks in its setup location to offer access control for network communication, whereas NAC manages communication between endpoints within a network. NAC, for example, can regulate a file share shared by two devices on the same subnetwork, although the firewall typically cannot.
Furthermore, a firewall often manages traffic by preventing non-compliant traffic from entering and exiting a network and operates on basic rule sets. NAC acts on the endpoints to regulate traffic between network devices more flexibly.
By addressing distinct areas of network control, NAC and firewall solutions complement one another.
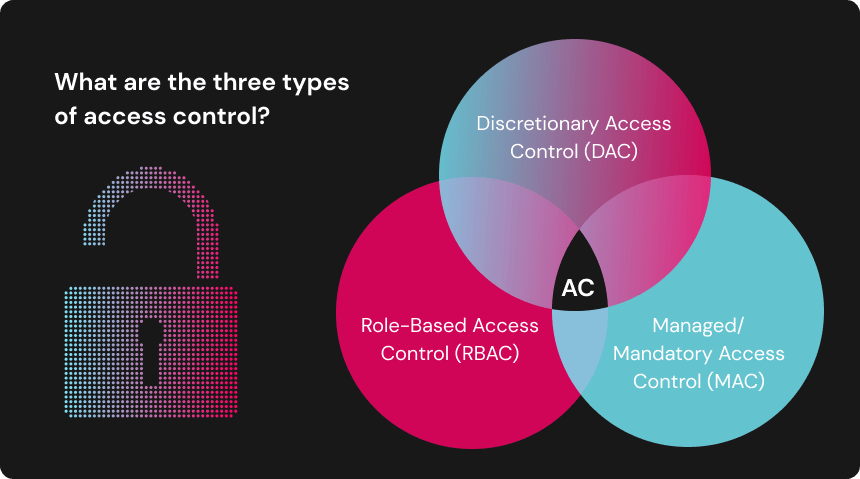
What are the three types of access control?
There are three types of IP Access Control
- Discretionary Access Control (DAC)
- Managed/Mandatory Access Control (MAC)
- Role-Based Access Control (RBAC)
Compared to its alternatives, Discretionary Access Control is exceedingly flexible and nonrestrictive.
This is because users choose their access rights. The owner of a corporation has the authority to determine who has access to the office space. Management can decide who gets access to which meeting rooms or portions of the facility. As a result, individual end-users have complete control over the buildings they own and the objects contained within them.
DAC is the polar opposite of Managed Access Control. It is also known as required access control because it gives the end user no control over their access to a facility. Only system administrators have the authority to grant or refuse access.
This means that owners must keep the permits of individuals with access to their buildings. They can only restrict access with the assistance of a professional, and they can only grant it to new people with authority. They also have no control over which places certain persons have access to.
Finally, the most popular solution today is Role-Based Access Control. This makes sense when you realize that RBAC combines the best characteristics of DAC and MAC.
Depending on the key holder’s role, the owner or system administrator assigns access to RBAC systems. Everyone is given roles and privileges based on their status. Their position also determines the constraints that will be placed on them.
Wrapping up
NAC is a great solution to monitor access on a closed network. Finding a NAC option that works for you can significantly improve your network security.